SSE and SASE within the Megaport Network
As organizations move toward cloud-native environments, the way organizations secure and connect their networks has fundamentally changed.
This topic explains the differences between Secure Service Edge (SSE)Security Service Edge (SSE) is a centralized, cloud-native security framework that converges multiple security functions into a single platform. It focuses on securing access to the web, cloud services, and private applications, regardless of the user’s location or device.
and Secure Access Service Edge (SASE)Secure Access Service Edge (SASE) is a security framework combining security and network connectivity technologies into a single cloud-delivered platform to enable secure and fast cloud transformation.
, and how Megaport provides the private and high-performance backbone to integrate SSE and SASE functions into your network.
Understanding SSE and SASE within the Megaport network
SSE – The security component
SSE is a set of cloud-delivered security services. It is designed to protect users and data regardless of where they are located.
- Key services – Secure Web Gateway (SWG)Secure Web Gateway (SWG) is a network security solution that filters unauthorized traffic and blocks malicious web-based threats. It acts as a protective barrier between an organization’s users and the internet, ensuring that web traffic complies with corporate security policies.
, Cloud Access Security Broker (CASB)Cloud Access Security Broker (CASB) is a security checkpoint which is deployed either on-premises or in the cloud, that sits between cloud service users and cloud service providers. It serves to enforce an organization’s security, compliance, and governance policies for all cloud-based resources.
, and Zero Trust Network Access (ZTNA)Zero Trust Network Access (ZTNA) is a strategic security technology that provides seamless and secure remote access to internal applications. Unlike a traditional VPN, which grants broad access to a network, ZTNA operates on the principle of “never trust, always verify.” It hides applications from the public internet and grants access only to specific authorized applications based on identity and context.
. - Goal – Secure User-to-App and App-to-App traffic.
SASE – The comprehensive architecture
SASE provides a comprehensive approach for networking and security. It represents the convergence of networking (SD-WANA software approach to managing and optimizing the performance of wide area networks (WANs). SD-WAN allows organizations to securely connect users, applications, and data across multiple locations while providing improved performance, reliability and scalability.
) and security functions into a single, global, cloud-native service.
- The formula – SASE = SSE + SD-WAN
- Goal – Simplify management and improve performance by combining connectivity and security.
As a Network as a Service (NaaS) provider, Megaport plays a critical role by hosting SD-WAN and security services. By providing a secure and private underlay as well as virtualized network functions (VNFs)Services responsible for handling specific network functions running in virtual machines on top of networking infrastructure.
hosting capability, Megaport enables the seamless integration of SSE and SASE features directly into your network architecture.
Megaport’s role – Connectivity layer
While SSE and SASE providers such as Palo Alto Networks, Cisco, and Fortinet manage the security inspection and policy, Megaport provides the private software-defined network that carries the traffic between your locations and the cloud.
Megaport bypasses the inherent instability of the public internet by utilizing a private and dedicated backbone. By using Megaport, you ensure your SSE and SASE traffic doesn’t get slowed down by public internet congestion and high-jitter or high-latency hops.
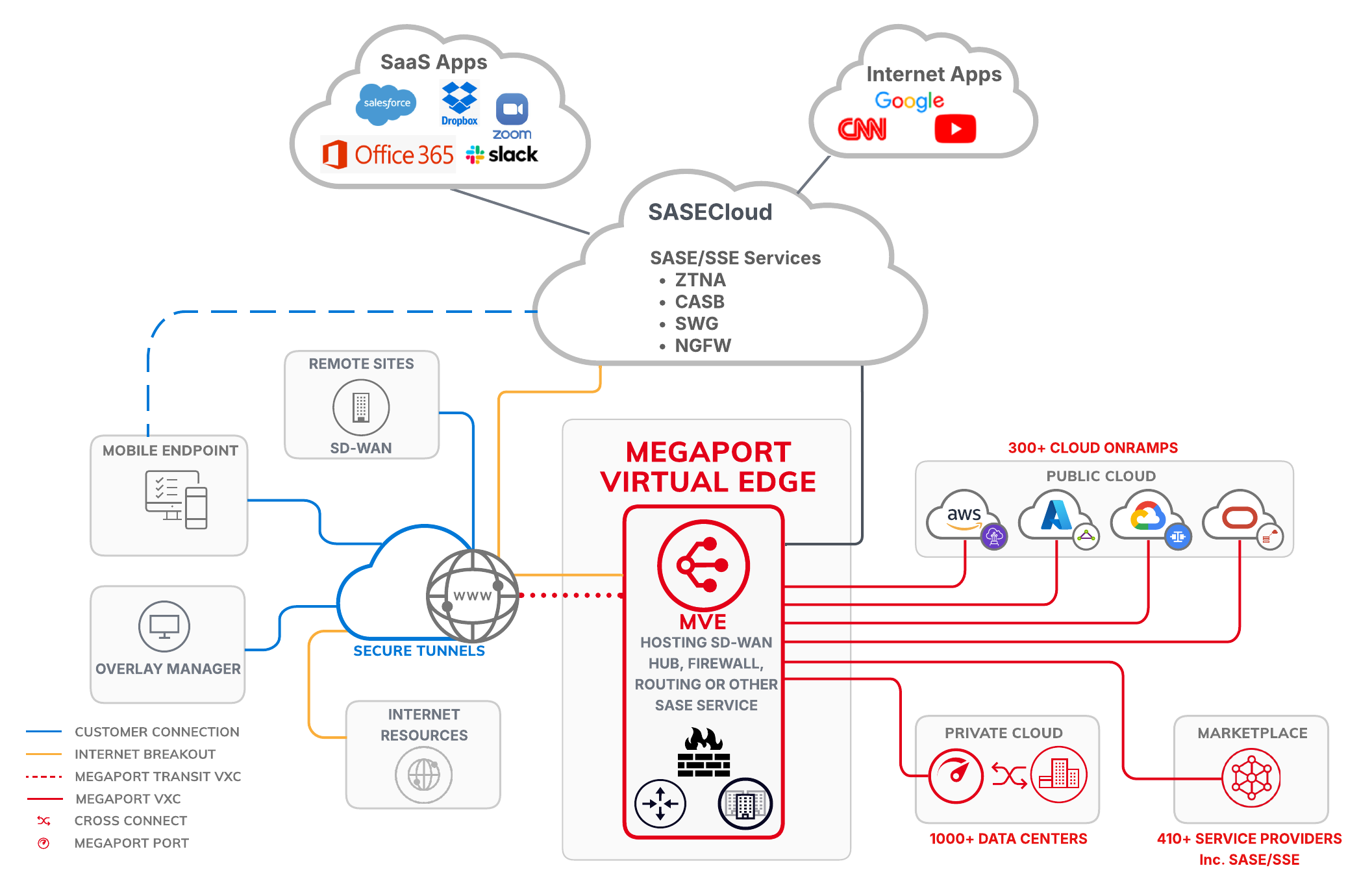
Network overview – SSE and SASE via the Megaport network
The following network diagram illustrates how the Megaport network carries private traffic to integrate SSE and SASE functions into your network.
Summary of features provided by SSE and SASE
The following table summarizes SSE and SASE features.
| Feature | SSE | SASE |
|---|---|---|
| Primary functions | Data and access security | Network + security |
| Common component | CASB, FWaaS, SWG, ZTNA | SD-WAN + SSE |
| User/branch deployment | Via a lightweight agent on the laptop or a browser portal | SSE Agent plus site-to-site and site-to-cloud tunnels automated by SD-WAN (Internet Protocol Security (IPsec)Internet Protocol Security (IPsec) is a secure network protocol suite for Internet Protocol (IP) communications that works by authenticating and encrypting packets of data in a communication session. It provides secure encrypted communication between two computers over an Internet Protocol network and is used in virtual private networks. / Generic Routing Encapsulation (GRE)Generic Routing Encapsulation (GRE) is a network tunneling protocol used to encapsulate a wide variety of network layer protocols inside virtual point-to-point links. It creates a private, direct path between two nodes across a public or third-party IP network. It wraps a data packet (the payload) inside another packet to transport it across a network that might not otherwise support the original protocol. GRE by itself is not encrypted. It provides a clear-text tunnel; for secure transmission, it is frequently paired with IPsec. ) |
| Vendor examples | Zscaler, Netskope, Cloudflare | Cisco, Fortinet, Palo Alto |
Implementing SSE using Megaport services
Architectural overview
Some SSE platforms, including Cloudflare, Netskope, Cato, and Palo Alto Prisma Access, integrate with Megaport by providing private connectivity to Megaport-enabled data centers and cloud on-ramps.
You can also implement SSE solutions with a Megaport Virtual Edge (MVE), which hosts virtualized network functions (VNFs) such as Next Generation Firewall (NGFW) Next Generation Firewall (NGFW) is a third-generation integrated network security platform that combines a traditional firewall with additional advanced filtering functions. Unlike older firewalls that only look at port and protocol (Layer 4), NGFW inspects the actual data within the traffic (Layer 7) to identify and block sophisticated modern threats.
, CASB, SGW, and ZTNA, at the edge of Megaport’s global private network. The MVE also facilitates secure access from cloud-based SSE platforms to private applications hosted in data centers and CSPs.
While SASE focuses on the convergence of SD-WAN and security, an SSE-centric MVE deployment prioritizes the security stack and serves as a private on-ramp to cloud security providers. Instead of sending sensitive corporate traffic solely over the unpredictable public internet, user traffic is directed to a localized MVE.
Deployment workflow
-
Provision the MVE – Deploy an MVE instance in the metro area geographically closest to your users or branch offices to minimize latency.
-
Appliance activation – Once the virtual appliance is active on the MVE, it is registered with your SSE vendor’s central management console (for example, Prisma Access Strata Cloud Manager, FortiSASE). This allows you to push granular security policies and identity-based access controls to the edge.
-
Establish connectivity – To complete the path, you configure Virtual Cross Connects (VXCs) from the MVE directly to your Cloud Service Providers (CSPs) or your SSE vendor’s cloud points of presence (PoPs).
This setup creates a secure private underlay where traffic is first secured on the MVE and then transported across Megaport’s private backbone.
This bypasses internet congestion, mitigates DDoS risks, and provides a more stable, predictable path for your SSE-protected data.
Implementing SASE using Megaport services
Architectural overview
You can implement SASE SD-WAN with MVE, which hosts SD-WAN virtualized network functions (VNFs) directly on Megaport’s global private SDN.
Instead of relying solely on the public internet, traffic from branch offices or remote users connects to a localized MVE. The MVE runs certified SASE or VNF appliances from partners such as Cisco, Fortinet, Palo Alto Networks, Versa, and so on, which integrate the SSE security stack with networking optimization (SD-WAN).
Deployment workflow
-
Provision the MVE – Deploy an MVE instance in the metro area geographically closest to your users or branch offices to minimize latency.
-
Configure security policies – Once the virtual appliance is active, it will automatically register and authenticate with the vendor’s central orchestrator to incorporate SD-WAN security policies. For example, Palo Alto Panorama and Fortinet FortiManager.
-
Establish connectivity – Configure VXCs from the MVE to CSPs such as AWS, Azure, or Google Cloud. This creates a connectivity where traffic is secured at the edge and then transported across Megaport’s private backbone, bypassing internet congestion and reducing egress costs. A 100% private underlay to key locations, such as an enterprise headquarters office or a manufacturing facility, can be created through Megaport’s private data center interconnects globally.
MVE vendor image deployment
The following table provides a list of documentation explaining how to deploy a host MVE for your chosen vendor. This is the first step before implementing SSE and SASE services.
As Megaport continues to add new vendors, if a specific vendor is missing, check the MVE Overview section for the most up-to-date list of supported vendors.
For detailed configuration steps, please consult the product documentation provided on each vendor’s website.
| Providers | Solution | Links |
|---|---|---|
| 6WIND Licensed Network Functions | SASE | Planning Your 6WIND Deployment |
| Anapaya | SSE | Planning Your Anapaya Deployment |
| Aruba | SSE, SASE | Planning Your Aruba EdgeConnect SD-WAN MVE Deployment |
| Aviatrix | SASE | Planning Your Aviatrix Secure Edge Deployment |
| Check Point CloudGuard | SSE, SASE | Planning Your Check Point Deployment |
| Cisco | SSE, SASE | Planning Your Cisco MVE Deployment |
| Fortinet | SSE, SASE | Planning Your Fortinet Secure SD-WAN Deployment |
| Juniper | SASE | Planning Your Juniper Deployment |
| Palo Alto Networks | SSE, SASE | Planning Your Palo Alto Networks VM-Series MVE Deployment |
| Peplink FusionHub | SASE | Planning Your Peplink FusionHub Deployment |
| Versa | SASE, SSE | Planning Your Versa Secure SD-WAN Deployment |